The National Cybersecurity Institute (INCIBE), through its Internet User Security Office (OSI), has launched this Wednesday a highly serious alert for a new phishing campaign that impersonates the identity of Iberdrola with the excuse of sending an invoice. The real goal is to distribute the Grandoreiro banking malware, also known as Zbot.
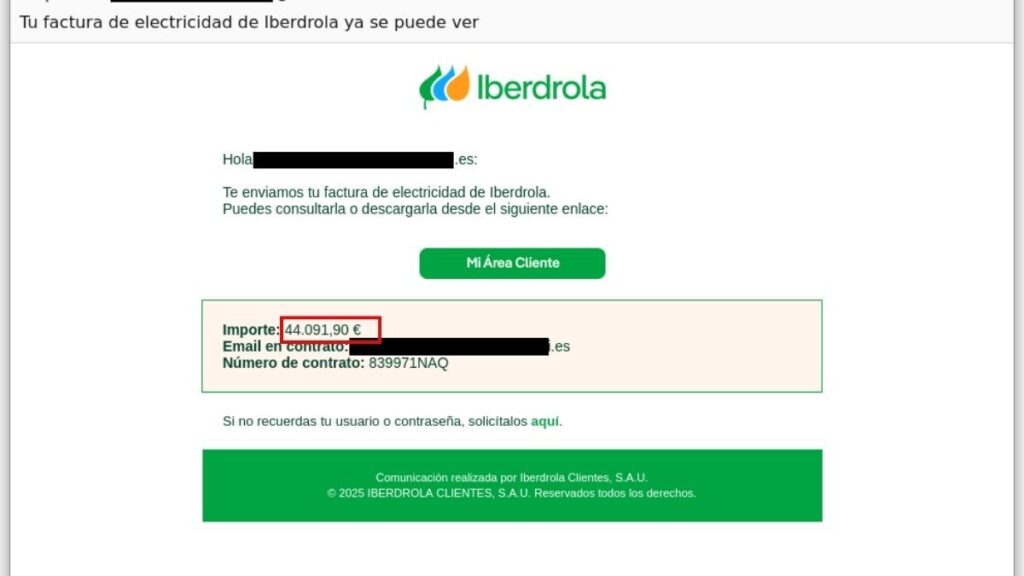
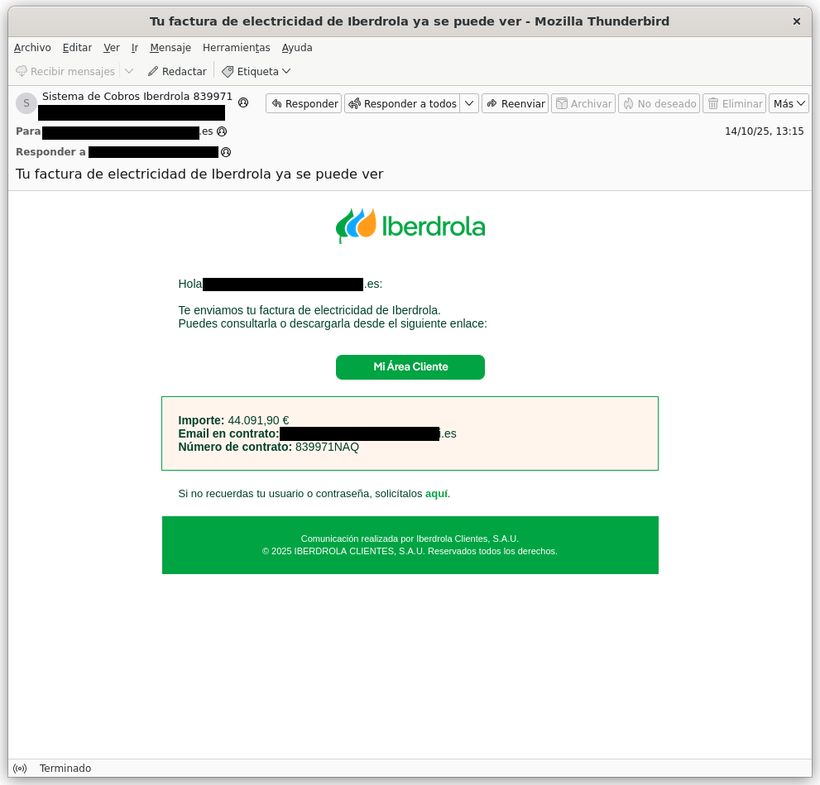
The scam is carried out through fake emails that imitate official notifications from the electric company. This is not the first time it has happened, since we have seen similar phishing campaigns that tried to imitate the identity of important entities such as the AEMET or Social Security to try to steal our private data. The fraudulent emails inform the user that their invoice is ready for consultation and include a link that apparently directs them to the customer area. However, upon clicking, a file with an .iso extension containing the malicious code is downloaded.
You may be interested
Civil Guard alert for Black Friday: if you receive this package from Amazon, call the authorities
BBVA forced to pay 5,977 euros to a client who was scammed by telephone: there were serious deficiencies in the bank’s control system
The trick to make people bite: put an exaggerated amount
According to INCIBE, cybercriminals use invoices with completely exorbitant amounts as a hook, ranging from 424.81 euros to 98,589.64 euros, to cause alarm and increase the chances that the victim will open the link. Furthermore, the email does not come from Iberdrola’s official domain and is addressed to the recipient using their email address instead of their full name, a detail that reveals the fraud.
Grandoreiro malware is designed to steal banking credentials, financial data, and other sensitive information. Once installed, it can cause system slowdowns, unusual browser behaviors, suspicious processes, and connections to unknown domains.
INCIBE advises that, if the user receives the email but has not clicked on the link, they mark it as spam, delete it and report it to the incident mailbox. If you have downloaded the file without running it, it must be deleted from the downloads folder and the trash. If the file has been executed, it is recommended to disconnect the device from the internet, perform a full scan with an updated antivirus and, if the problem persists, format the computer after making a backup copy of important data.
Likewise, it is suggested to save evidence of the attempted fraud, such as screenshots and the email received, to facilitate a possible report to the State Security Forces and Bodies.
For its part, Iberdrola remembers that it never requests personal or banking data by email or SMS, and invites users to verify any communication through its official channels.